This site uses cookies to store information on your computer, which provides functionality to our site and assists in providing our service. For more information see our Cookie Policy here. Please click "I Accept" to agree to our use of cookies.
Remotely Verify Identity with a Compliant, Easy-to-Integrate Solution
Verifying an individual’s identity is the first step in establishing that person’s eligibility to receive digital services. Today, it’s a complicated process. Citizens must create a new login with a unique username and password to access each website. This means more passwords, higher vulnerability, and increased risk.
ID.me securely verifies an individual’s identity in just minutes. Through remote verification of physical IDs, mobile network operator (MNO) data, along with fraud and compliance checks, ID.me’s federally-accredited platform is transforming the way citizens access services online.
How it works
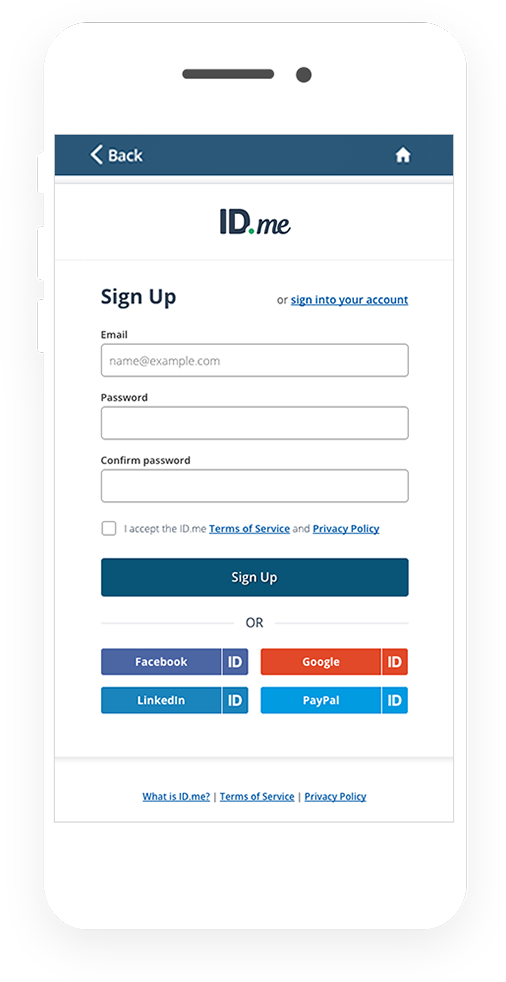
The user creates an ID.me account, which they’ll use going forward to log in to the website.
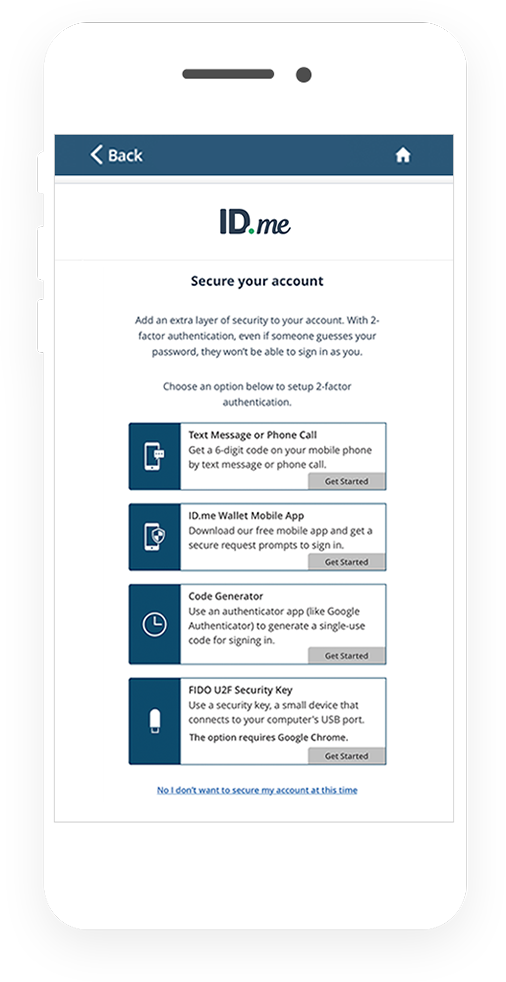
The user protects their account from takeover with Multi-Factor Authentication using one of the following options:
- Enhanced SMS
- Phone call to landline
- ID.me Authenticator App
- Security key
- Code Generator
The user takes a photo of their driver’s license, state ID, or passport to verify their identity.
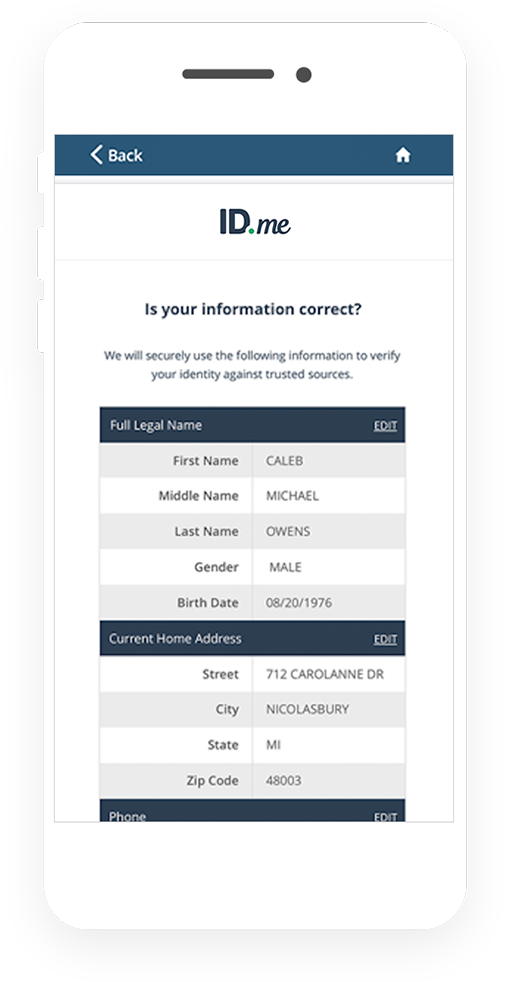
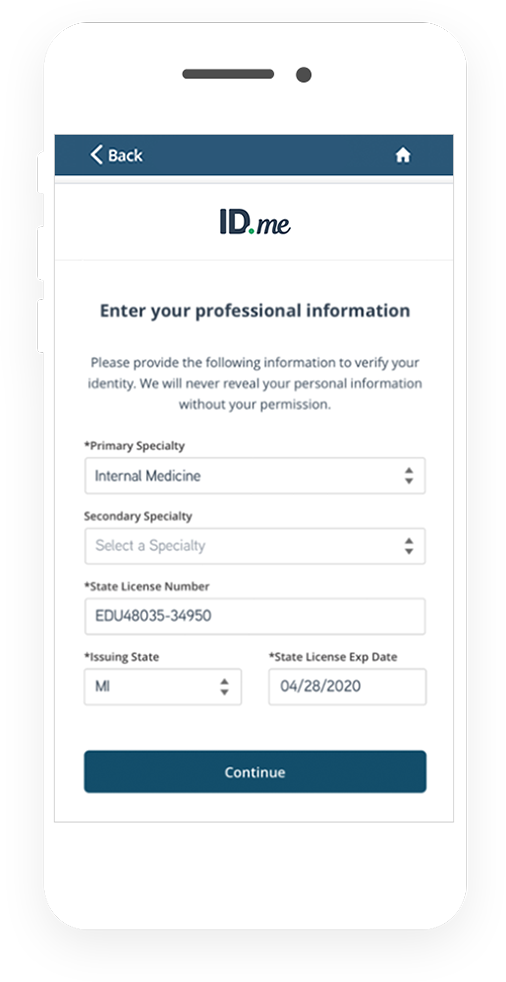
Data extracted from the document pre-fills form. The user confirms the data and adds their SSN.
A verified ID.me credential is created.
Why Organizations Choose ID.me for Online Identity Proofing
NIST 800-63-3 Aligned
Meet IAL2/AAL2 identity proofing and authentication standards to comply with federal and state-level requirements.
Interoperable Login
Once a user has verified their identity with ID.me, that person will never have to re-verify their identity again across any organization where ID.me is integrated.
Easy to Deploy
ID.me's identity broker makes it easy for organizations to consume multiple third party IDPs and strengthen legacy logins.