This site uses cookies to store information on your computer, which provides functionality to our site and assists in providing our service. For more information see our Cookie Policy here. Please click "I Accept" to agree to our use of cookies.
Why is NIST-Compliant Identity Proofing Important?
The National Institute of Standards and Technology (NIST) drafts and publishes the digital identity standards that organizations use for identity proofing and authentication at different levels of risk.
ID.me’s NIST-compliant identity proofing solution can issue IAL2 / AAL2 compliant credentials to provide access to high-risk services. The verification process is simple and fast, and users only need to do it once to create their NIST-compliant credential.
ID.me's NIST 800-63-3 IAL2/AAL2 Credentials
How It Works
Step 1:
Multi-Factor Authentication
Secure accounts with Multi-Factor Authentication (MFA) options designed to accommodate all kinds of users.
Step 2:
Remote Document Verification
Scan driver’s licenses, state IDs, and passports, and apply machine vision and AI to verify authenticity.
Step 3:
Face Match
ID.me uses facial recognition to match the user’s selfie to their uploaded government ID.
Step 4:
Mobile Phone Verification
Verify that the SIM in the mobile device used for the verification is associated with the applicant’s identity and screen for potential indicators of fraud.
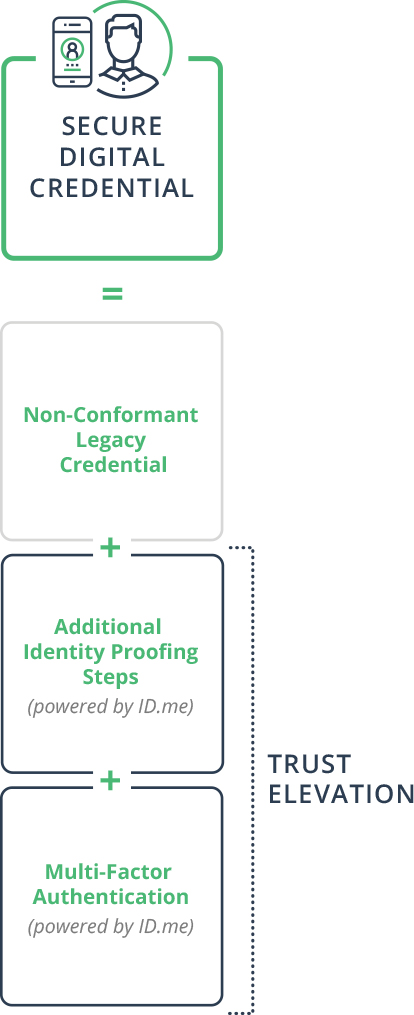
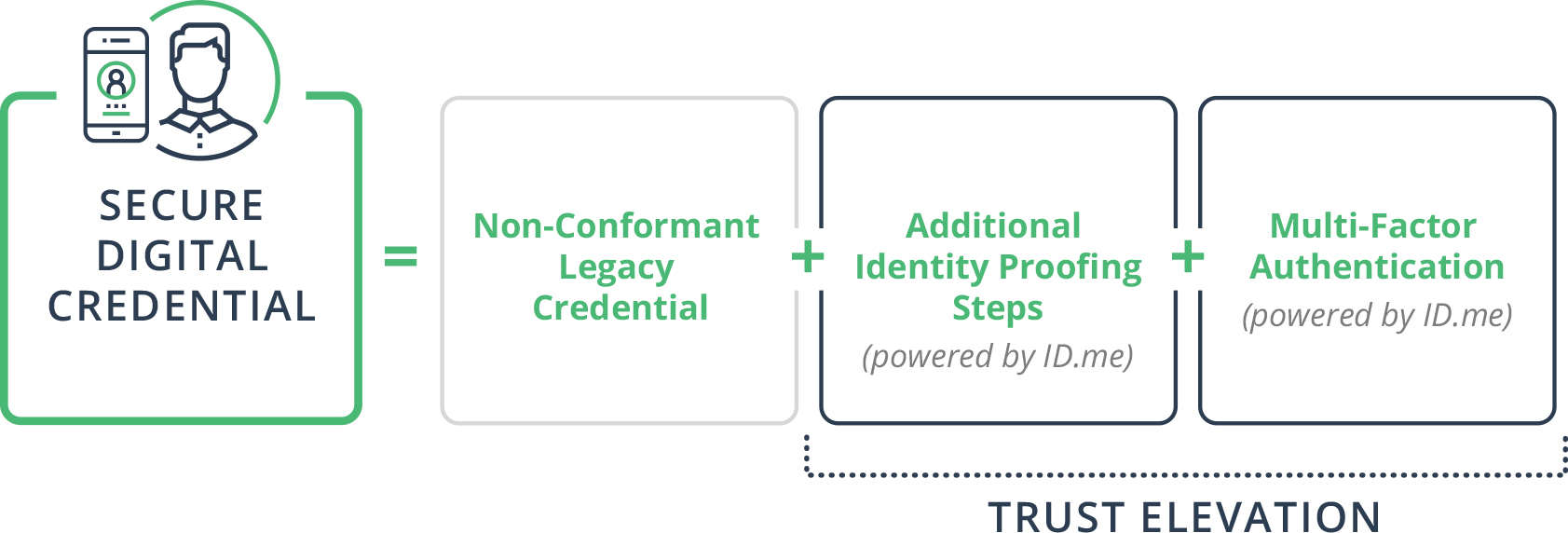
strengthen legacy logins with trust elevation
To help organizations make legacy logins conformant with NIST standards, ID.me adds additional identity proofing steps or Multi-Factor Authentication ensuring citizens can continue to use familiar logins.
Why Organizations Choose ID.me
Online, Virtual In-Person, and In-Person Proofing
Support both online self-enrollment, in-person proofing, and virtual in-person proofing. Front-line and call center staff can use the referee app to enroll users who are unable to complete the identity proofing process online.
Trusted Referees
Trained and certified call center employees called Trusted Referees guide users through the identity proofing process over video chat.
Easy to Deploy
ID.me's identity broker makes it easy for organizations to consume multiple third party IDPs and strengthen legacy logins.
Keeping your information safe
ID.me is a digital platform that helps people like you easily prove your identity so you can access online services and benefits online. This is to help make sure you’re you—and not someone pretending to be you.
ID.me provides the strongest identity verification system available to prevent fraud and identity theft. We use bank-grade encryption to keep your personal information safe. And you control which services and businesses you share your information with, always giving your explicit consent.
Hundreds of well-known private-sector companies (such as Linkedin, Ford, Apple, and USAA) and government agencies (such as the U.S. Department of Veteran Affairs) have also chosen ID.me to help keep their customers’ personal information safe.
More questions?
Check out our FAQ.
